This post is written from the perspective of an Information Technology team supporting the business in running their eDiscovery requests.
Before diving into the details of eDiscovery, check out the first post in this series where I share the importance of having well established Information Governance practices in your organization as a foundation for running effective eDiscovery cases. You need to ensure your organization’s data is compliant with your own regulatory, legal, and contractual obligations.
Link: Building the Foundation for Office 365 eDiscovery
This is a joint post with my friend and co-worker, Ali Fadavinia.
Ali’s technical background is Cloud, Network and Computer Software Engineering. He enjoys working with cutting-edge technologies and implementing them across infrastructures and organizations. He works with the Azure and Office 365 suite of products such as Microsoft Teams and Skype for Business in his daily work.
You can reach out to Ali via LinkedIn.
Now that we have our electronic house in order by laying a strong information governance foundation, we’re ready to move on to executing eDiscovery cases in our tenant. eDiscovery (Electronic Discovery) is the process of identifying and delivering electronic information to be used as evidence in a legal case. In Office 365, there are two variations of eDiscovery, each available thru different licensing:
- Core eDiscovery: E3
- Advanced eDiscovery: E5 or E3 with Advanced Compliance add-on
An eDiscovery case can address an internal investigation, external litigation, or a regulatory request. In this post, we’ll demonstrate how an organization can set up their eDiscovery teams and roles by walking thru an internal investigation example.
Scenario: A finance employee at Contoso was caught sharing the latest financial report with a competitor. Contoso’s internal audit team has requested an investigation be launched to determine all activity relating to this breach for this employee.
The goal of eDiscovery is to provide evidence of this behavior by finding all relevant content relating to the breach.
The first thing to address is how to set up permissions for managing the eDiscovery case workload across your organization. To demonstrate how we will assign eDiscovery roles to manage this case in Contoso, the image below shows the eDiscovery permission model for the business teams across Contoso who are involved in eDiscovery cases. In this example, the Compliance Oversight team oversees all eDiscovery cases in the Contoso tenant and is therefore assigned the eDiscovery Administrator role. Each of the teams under Compliance Oversight participate in eDiscovery cases for their own organizational unit and are only allowed to see their own cases. To accomplish this, we assign either an eDiscovery Manager or Reviewer role to members within each of those teams to allow them to work on their eDiscovery case(s). This means, for example, Legal can’t see HR’s cases and HR can’t see Legal’s cases. This is an important requirement for many organizations since some eDiscovery cases may deal with sensitive and highly confidential information.

Note: if there is a requirement for isolation between case managers to control the user content locations each of them have available for search, you can configure Compliance Boundaries. This may be a requirement in some organizations where there are regulations specific to a geographical boundary or company location. Reference: Set up compliance boundaries for eDiscovery investigations in Office 365.
For our internal investigation example and using the team structure above, we’ll assign the following roles for this case:
Several members of the Compliance Oversight team will be assigned the eDiscovery Administrator role. They will assign other eDiscovery managers and reviewers across Contoso’s case workload and will have oversight into all cases.
The Internal Audit team lead will be assigned the eDiscovery Manager role.
Additional Internal Audit team members will be assigned either an eDiscovery Manager or Reviewer role based on their duties for the case.

Note: the eDiscovery reviewer is the most restrictive eDiscovery role. This role allows you to review a case, view search results and export results. This role cannot place content holds nor create content searches. This role may only be required in large eDiscovery cases.
Steps for the creation and management of this case:
1. Internal Audit team lead creates the case.
Tip: Come up with a naming standard for your cases. Over time, you will accumulate a large # of cases (particularly if you never delete them) so a naming standard will help with case administration. You can also use this case name to tag any documents you’re storing in SharePoint to administer the case.
Example: “Internal Investigation 2019-123”
2. Internal Audit team lead adds other Internal Audit team members as eDiscovery managers or reviewers to the case to help with the review and analysis. (optional) Whether this is done or not depends on the size and nature of the case. The team decides on the type of communication they will be searching for in this case: the employee’s email as well as the files on their OneDrive.
3. The OneDrive and Outlook mailbox of the employee(s) being investigated are put on hold. (Note: the person(s) whose content is put on hold is called a custodian)
When OneDrive is on hold: this creates a ‘Preservation Hold library’ on the custodian’s OneDrive. The custodian will be able to continue to add/change/delete content on their OneDrive while the hold is in effect.
When Outlook is on hold: the Mailbox Folder Assistant job will stop running for the custodian’s mailbox preventing any email from being permanently deleted while the hold is in effect.
The custodian will be unaware of either hold unless they are informed of it. In Advanced eDiscovery, there is a built-in option to manage this communication as sometimes it’s required.
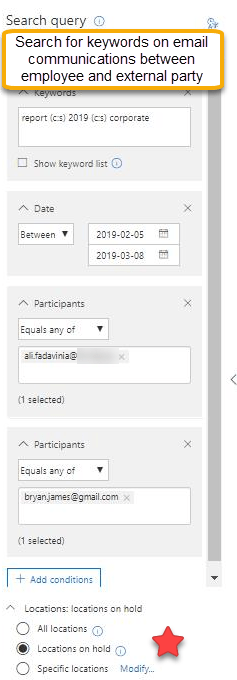
4. Any of the eDiscovery managers can build an eDiscovery search and run it against the hold locations to detect all suspicious activity between this Contoso employee and the competitor. In this example, we’re searching for keywords: report, 2019, or corporate between the 2 parties for a date range.
5. If using Core eDiscovery, the eDiscovery team will export the results for further review and analysis. Because we searched against the hold locations, there will be 2 types of output:
OneDrive: a folder structure for content in the employee’s OneDrive is built and can be exported to a file location for review.
Outlook: you can export either 1 .pst file or individual email messages for the employee’s mailbox. It will return all emails with the search term in the title, body, or attachment of the message.
6. If using Advanced eDiscovery, the eDiscovery team will review the results within the tool itself using review set(s). This allows reviewers to query the results, view threaded emails and document families, use custom-defined tags to cull unnecessary content and identify relevant content, and even redact sensitive/confidential information. Once ready for preparation, the results can be de-duped and exported to an Azure blob storage location.
7. Depending on the requirements of the case, the relevant results from the eDiscovery will be prepared for external review/presentation by the eDiscovery team. The output of the electronically stored information (ESI) can be downloaded in Native format.
8. Case closed. The eDiscovery Administrator may choose to release the holds on the custodian (will depend on the nature and status of the case) and set the overall case status to closed.
Closing thoughts
It’s important to have a plan in place for how your organization will structure your eDiscovery cases across your tenant for business teams executing them. The intent of this post was not to be prescriptive on how to set up your teams, but to provide one example of doing it. Organize your own business teams’ eDiscovery roles in a way that makes sense for your org structure aligning each team with the types of eDiscovery case they’re responsible for.
Thanks for reading.
-JCK and Ali
Image: Photo by Hasan Albari from Pexels

